I’ve written about IoT threats in the past about Huwaei Gateways, Netgear routers, and IP cameras, but this time I’m covering the must-have device over the past couple years. Smart speakers.As I’ve said in previous articles, the more convenience that’s designed into a product that connects to the internet the higher the likelihood of an attacker exploiting that device.
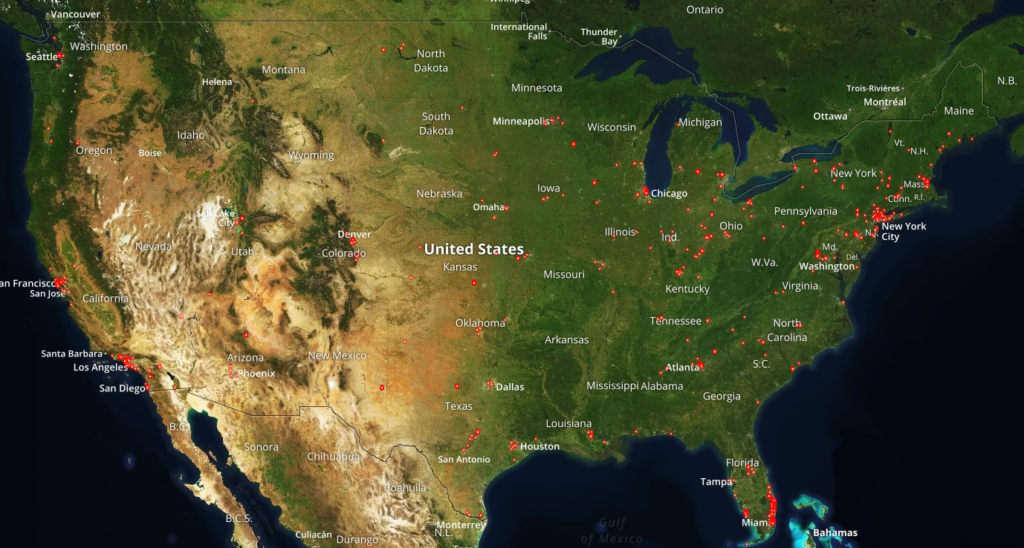
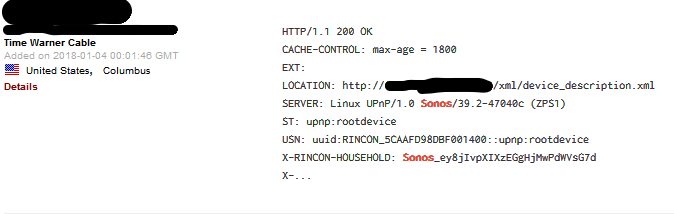
Researchers at TrendMicro have released findings on two new smart speakers that are also high fidelity. The Sonos Play:1 and the Bose SoundTouch can be detected online with a simple internet search tool. Shodan allows you to see the geographic location of each device on a map and reveals the port on which the device has open to the Internet that anyone can access that knows the IP address and port. It’s easy to go online to the manufacturer website and find the port the speakers run on for troubleshooting.
There are 4,776 Sonos speakers that are Internet accessible in the United States.
Previous studies focused on taking over control of Alexa and Google home devices with ease along with a Bluetooth vulnerability that provides another avenue in which attackers can record you without you knowing. Thankfully, smart speaker and cell phone manufacturers have patched the Bluetooth bug.
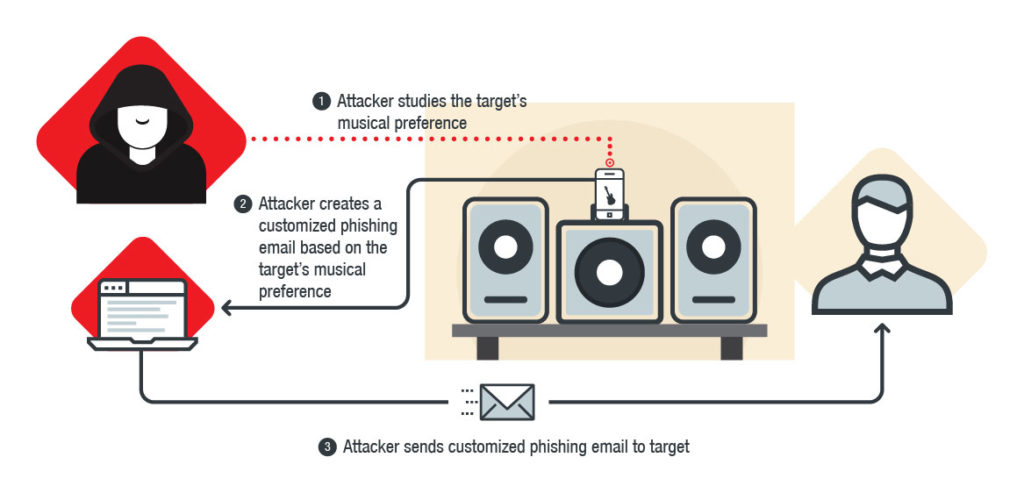
The TrendMicro study is unique in that it doesn’t seek to outright control the device, just what audio it will play and which information can be gathered from the devices.
The author of the study, Stephen Hilt, says “Whereas previous studies focused on seizing control of speakers like the Amazon Echo and Google Home, the results of our case study led to unique findings. These include security gaps that resulted from a simple open port that gave anyone on the internet access to the device and user information,” and adds “The first glaring finding was access to email addresses that are linked to music streaming services synced with the device. Another was access to a list of devices as well as shared folders that were on the same network as the test device.”
The researchers were also able to geographically locate their test device and see the devices activities such as current song playing.
The good news is that Sonos has already issued a patch and as long as you are keeping your Sonos Controller updated you should no longer be vulnerable to the remote commands and information disclosure.
Source: cyberscoop, TrendMicro