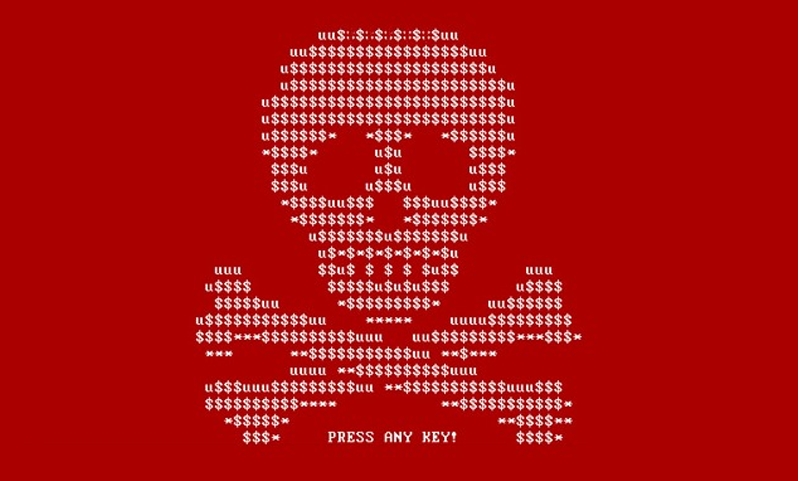
Ransomware Deployment Protocol (RDP)
RDP stands for Remote Desktop Protocol that is used by people that need to access the desktop of a remote Windows computer. Hackers have been gaining access to these remote machines for over a decade thanks in part to weak passwords that are used to “secure” them by just guessing the username and password. Once... Continue reading Ransomware Deployment Protocol (RDP)