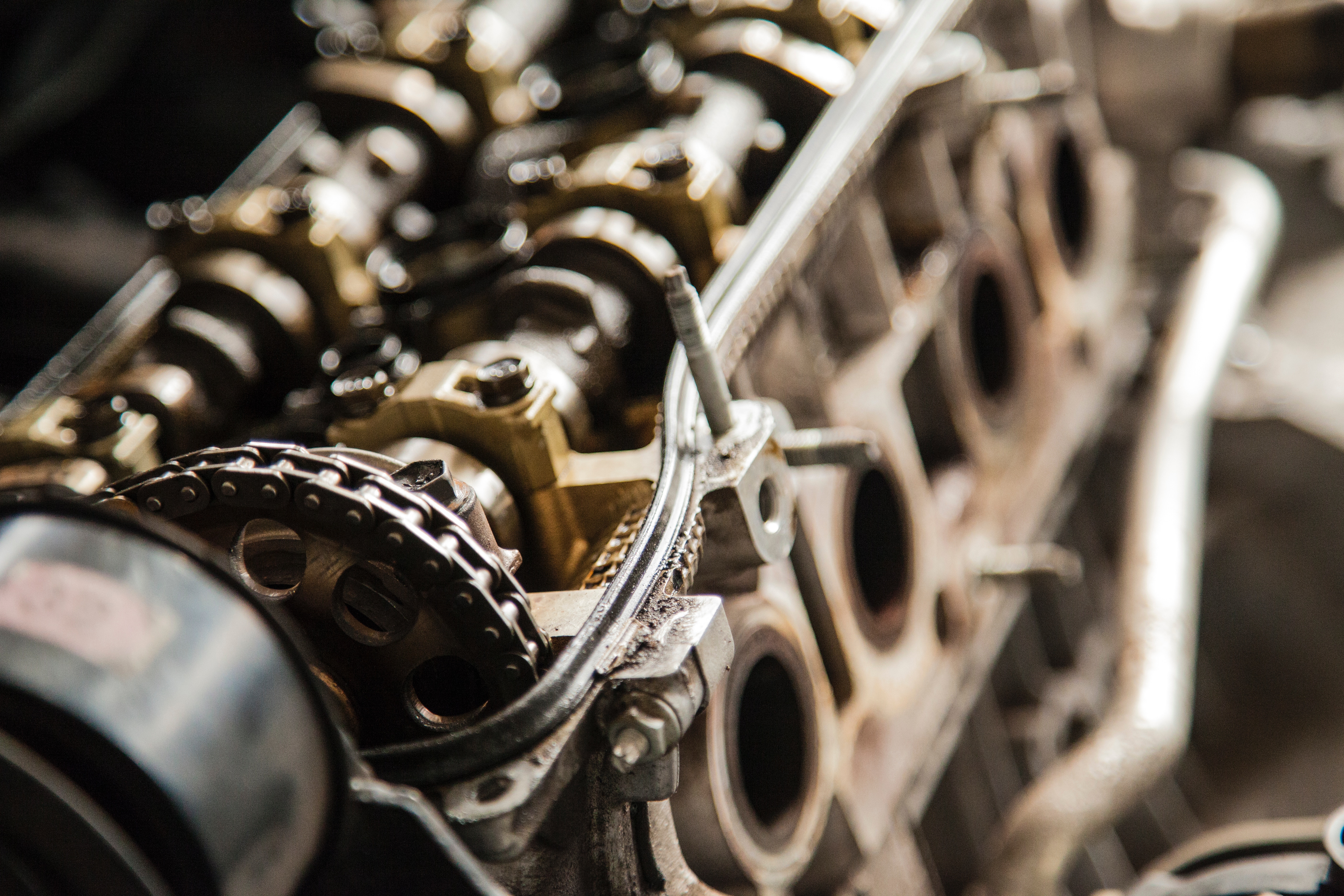
Get it right or get out of the way
When a company has a break down in its processes blame is assigned based on whom the process owner is and the individual(s) responsible for completing the missed or an improperly executed task. When a low-level process is broken such as the case was with Experian and the missing Apache Struts patch that allowed an attacker to gain... Continue reading Get it right or get out of the way