When a company has a break down in its processes blame is assigned based on whom the process owner is and the individual(s) responsible for completing the missed or an improperly executed task. When a low-level process is broken such as the case was with Experian and the missing Apache Struts patch that allowed an attacker to gain a foothold in their information system and steal 152 million records, I see little reason to start chopping off the heads of senior leadership. Processes should be reviewed at a regular interval that is appropriate for the businesses operational environment (annually, semi-annually, quarterly, or monthly). In Experian’s case, I believe there was a systematic breakdown where the process was broken, and no one up the chain of command was notified. A CIO and CSO at a company as large as Experian don’t have the time or resources to personally check-up on every department nor should they be required to micro-manage. Mid-level and upper-level management should be feeding data to the C-suite at their meetings and if something was off or missing it should’ve been addressed.
Experian’s Chief Information Officer (CIO) David Webb and Cheif Security Officer (CSO) Susan Mauldin shouldn’t have been fired, albeit, the press release said “retired.” The process owner, which is typically a manager if there isn’t a dedicated process team like with Lean and Six Sigma, and the person performing the task should’ve been fired. From what I understand the overall security program health of Experian was good (adequately funded, risk assessments were regularly conducted, gap analysis, etc.). The personnel that was directly responsible for the patching went unreprimanded or were reassigned.
All security programs have issues, and the failure in Experian’s security program was catastrophic. The firing of the CIO and CSO was purely a PR move, and the flak that Susan Mauldin and Experian took for Susan having a music degree was uncalled for, because experience, not a degree, should play a more significant role in determining the qualification for a position. Finger’s were pointed everywhere because 1) the sheer weight of what happened and 2) most media relations departments don’t understand how to communicate issues about technology. I’ve seen PR do more harm than good when it comes to data breaches.
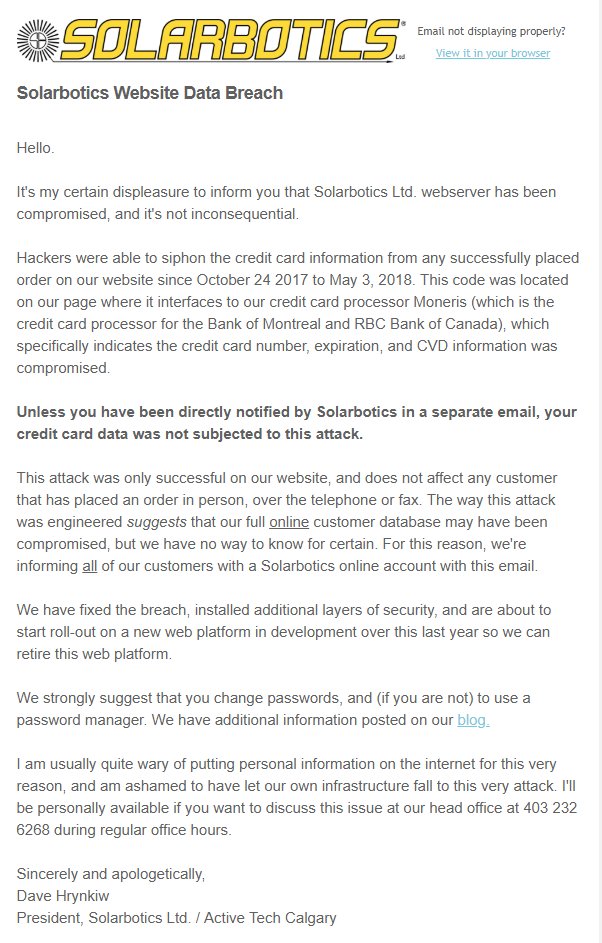
When it comes to disclosing a data breach publicly, it’s best to keep the initial statement concise, honest, and open-ended.
T-Mobile has had two issues with their website improperly disclosing customer information. The first issues was around September of 2017 that allowed anyone that knew or could guess someone’s phone number to run “a script to scrape the data (email, name, billing account number, IMSI number, other numbers under the same account which are usually family members) from all 76 million of these customers to create a searchable database with accurate and up-to-date information of all users,” according to the researcher that discovered the vulnerability in an article by Motherboard. The UnCarrier stated that a small portion of their customers was affected and (emphasis added) “we were alerted to an issue that we investigated and fully resolved in less than 24 hours. There is no indication that it was shared more broadly.”
T-Mobile later followed with “excuse me, it’s 70 million customers.”
The problem with the last sentence of their statement is that they didn’t do their homework. Media Relations and lawyers signed off on that statement. Tutorials were uploaded by black hat hackers to YouTube on how to exploit the vulnerability which existed because they didn’t use input validation and the true extent of exploitation can’t be determined.
The second issue came to light in December of 2017 that permitted hackers to log in as any T-Mobile customer and allowed changes to be made to the account that an authenticated customer would be able to make. In another article by Motherboard Scott Helme said that T-Mobile should have reviewed logs to see if the vulnerability was exploited. Unfortunately, T-Mobile doesn’t offer much confidence in their statement that is similar to the issue in October of 2017 by saying “if there had been customer impact we would have immediately taken proper steps to follow up.”
T-Mobile was fortunate that these two issues weren’t widely exploited (as far as what is known) and we avoided another Experian-like disaster.
Media Relations departments like to tell people what they should think or feel instead of which steps and actions were taken so the reader can be informed. There are many great journalists such as Ryan Naraine, Zack Whittaker, Patrick O’Neill, Selena Larson, and others that decode PR bullshit and call companies out on their lies and “half-truths.” You can call them vulnerabilities and use critical or any other severity identifier all you want, but to non-technical people, there isn’t a proper interpretation because they don’t have knowledge of weighted criteria, so companies get away with having little pressure to do better.
If all the CEO, Media Relations, and the lawyers want to do is be as vague as possible then get out of the way and let the CIO, CISO, or CSO do right by their profession and be honest about what happened while maintaining operational security.
The image below is the ideal way to approach announcing to the public that your company has been compromised. It’s honest and to the point.