Do you remember the Mirai botnet?
If you don’t, here’s a quick refresher.
Mirai is an internet-of-things malware that turns DVRs, security cameras, toasters, refrigerators, etc., into a zombie that can attack another network or device with a flood of empty data that will overwhelm and cause a denial-of-service (the device or network loses internet connectivity). You can find more information on Mirai and a different species of IoT malware called IoTroop here.
Mirai is back in a new flavor and has infected approximately 100,000 devices. Mirai has 65,000 usernames and passwords stored in it to increase the likelihood of successfully accessing devices because people are bad at creating unique passwords and rarely follow sound guidance and set themselves up for failure then get mad at other people for what they did.
You’re in luck with this version of Mirai because even if you have a strong password and have remote management disabled, the malware can still infect your device using a recently discovered zero-day vulnerability, so this time you have not caused your demise, and we can blame the software developer – Huawei.
Huawei’s EchoLife Home Gateway and Home Gateway are the two most targeted devices accounting for 90% of the infections. Naturally, I turned to Shodan to see the spread of these devices across the world and to get a total number of devices against the number that has been infected to determine the overall potential for how large this new Mirai botnet can get.
Huawei EchoLife Home Gateway
Top Four Country's
Mexico 65,297
Columbia 1,949
Algeria 1,550
Peru 410
Global Total 70,779
Huawei Home Gateway
Top Four Country's
China 25,009
Mexico 4,009
Hungary 3,707
Thailand 3,100
Global Total 44,868
The total for the two devices worldwide is 115,647, so the botnet has some room to grow. Keep in mind that the numbers in the tables don’t include devices that were offline (powered off, disconnected, not in use) when I made the search query.
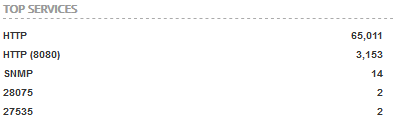
Internet access for the EchoLife is primarily through port 80 which is used for unencrypted web pages.
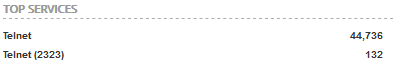
 Internet access for the Home Gateway is only through Telnet that is also unencrypted communication.
Internet access for the Home Gateway is only through Telnet that is also unencrypted communication.
 Not only did the software developers for Huawei do a poor job of writing secure code (in their defense bugs always happen, but a 0-day is especially bad) they also force the users to use insecure communication for remote management.
Not only did the software developers for Huawei do a poor job of writing secure code (in their defense bugs always happen, but a 0-day is especially bad) they also force the users to use insecure communication for remote management.
Internet-of-things manufacturers must do a better job at writing secure code because botnets will continue to grow larger and as a result pose an even more severe threat to the stability of the Internet.