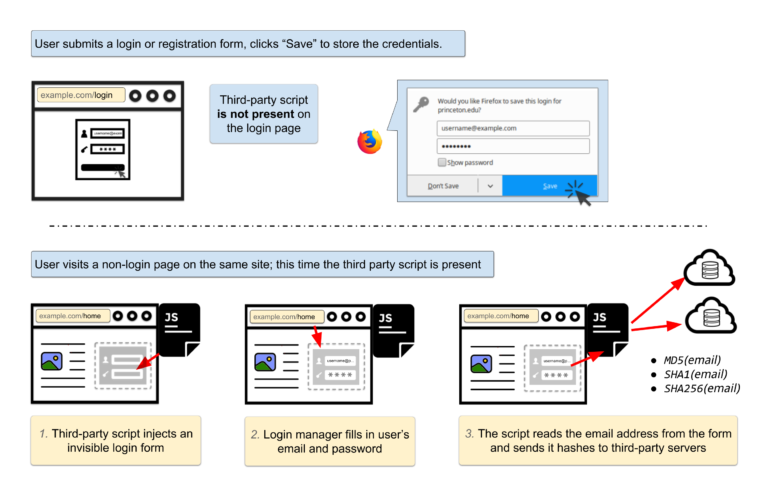
Browsers give you the option of auto-filling your username and password as a convenience, but convenience usually comes with vulnerability in the cyber world, and this is no exception. There are two scripts used by over one thousand websites to steal your email address and other user identifiers to send to third-party servers to track you.
Site owners are using one of two scripts that are an invisible login form that recognizes that your browser is using auto-fill.
The researchers from Princeton examined 50,000 websites and were pleased to find that there were not any cross-site scripting shenanigans outright stealing usernames and passwords. In case you are not aware, your browser credential manager is vulnerable to theft with alarming ease which you can read about here, here, and here.
You might be asking yourself what the big deal is about your email address being sent to servers without your knowledge. Gunes Acar, one of the Princeton researchers and author of the article, explains “Email addresses are unique and persistent, and thus the hash of an email address is an excellent tracking identifier. A user’s email address will almost never change — clearing cookies, using private browsing mode, or switching devices won’t prevent tracking,” and adds “The hash of an email address can be used to connect the pieces of an online profile scattered across different browsers, devices, and mobile apps. It can also serve as a link between browsing history profiles before and after cookie clears.”
The descriptions for the two login stealing scripts are “Smart Advertising Performance” and “Big Data Marketing,” and are owned by Adthink and OnAudiance respectively.
If you want to check whether your browser is vulnerable by testing if the built-in credential manager will auto-fill an invisible login form you can visit the online demo. Make sure you use a fake username and password.
Source: Freedom To Tinker