The hacking group Anonymous came to the forefront of America’s consciousness in 2008 when they took on the Church of Scientology. Anonymous is known as a hacktivist group in which they create operations or projects for specific activist causes. Of all the operations, Operation Child Safety and other pedophile hunting teams discover the most gruesome images that can quickly cause mission fatigue, but they press on.
The history of Anonymous
Anonymous got their name from 4chan in 2003. 4chan is a forum that was modeled after 2channel, a popular bulletin board website in Japan, in the same bulletin board fashion. People that post on 4chan can have usernames, but many forego a username and post under the name anonymous. Most of the content on 4chan is random and is credited with the creation of many popular memes that are both good and bad.
Some of the Anonymous causes include:
- 2008: Project Chanology
- 2009: Project Skynet and Operation Didgeridie
- 2010: Operation Titstorm, Operation Payback, and Wikileaks
- 2011: Arab Spring, HBGary Federal, GeoHot, and Occupy Wall Street
Project Chanology is when Anonymous received the most media attention in its history. The goal of Chanology was to bring to light the abuses of the Church of Scientology against members that left or were trying to leave the cult.
On January 14th of 2008, a video was leaked from Scientology on YouTube that had Tom Cruise laughing hysterically and rambling nonsensically. Scientology tried to get YouTube to remove the video based on copyright infringement but was unsuccessful. Anonymous released a video addressing Scientology after they were threatened.
The video is embarrassing.
Anonymous held protests against Scientology with members wearing Guy Fawkes masks, like the one in the feature image, from the movie V for Vendetta to protect their identity’s. It was necessary to protect their identity’s because Scientology has a long history of conducting smear campaigns against people that oppose them.
The majority of Anonymous operations involve denial-of-service attacks and publicly releasing information on people and organizations that are called doxxing. The information obtained for doxxing is done through legal means called open source intelligence gathering and illegal means such as hacking a database.
Pedophile hunting operations
An operation that I’m going to cover in detail in this article has been active circa 2014 and is known by many names but started as Operation Pedophile Hunt or OpPedoHunt as Anonymous calls it. The first contact I spoke with inside of Anonymous, whose real name I never asked for considering the sensitive nature of this business, is #OpChildSafety, his Twitter handle and goes by P3SH within Anonymous. P3SH described how OpPedoHunt began in an email, “The creator of OpPedoHunt started it over four years ago, sometime when #twittergate happened and 0hour exposed @jack for having cp content on his IG account and allowing it on twitter platform.” Jack is the CEO of Twitter.
P3SH has given me a deep look into the world of pedophile hunting, and, surprisingly, there are potentially hundreds of people in the hunt for offenders. “I couldn’t give you a specific number, but there are many, there are more pedo hunter groups out there than just mine and oppedohunt, there’s OpDeathEaters, they have many branches like OpDeathEatersUk, Au, etc., there’s OpStopPedo, OpPedo, OpFocusHunters, and there’s more on Facebook, names I’m not even familiar with, the ones on Facebook actually do a live feed and catch pedos trying to meet up with underage children,” said P3SH in an email.
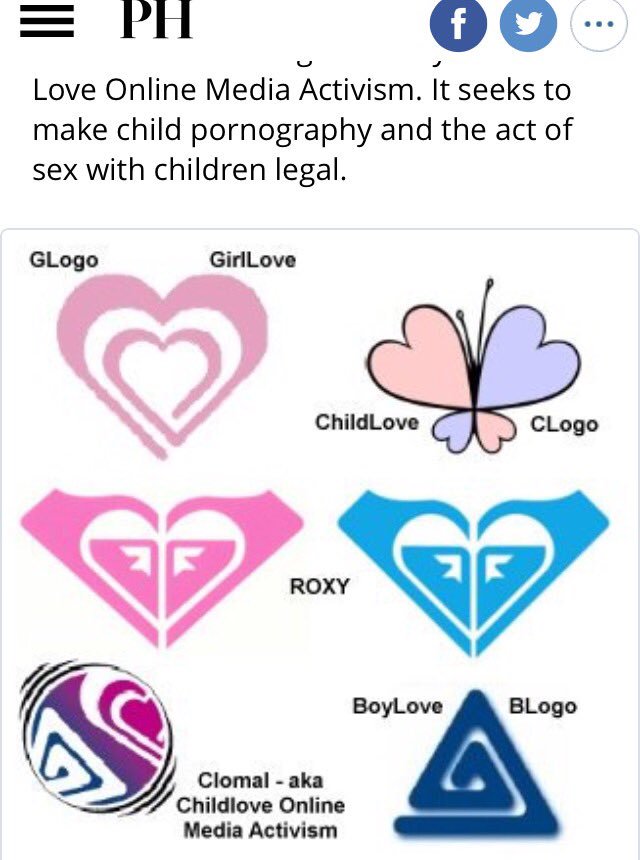
These pedophile operations involve finding social media accounts that distribute or request child pornography. P3SH said, “I don’t as much as I know [sic] another who does, that requires a lot of time, which I don’t have much of, unfortunately, not sure of all the platforms, I’m sure if sought out they can be found on every platform.”
If you know what to look for you can find offenders on nearly all social media platforms. P3SH told me in an email that, “On Twitter, targets will sometimes post their WhatsApp numbers, kik, gab, etc., and that’s maybe all they are posting, but when checking them on other platforms, we may find the cp there, so more or less its investigating.”
I was added to the group message for OpChildSafety, called the OpChildSafety Support Group, on Twitter, and it’s an endless stream of accounts distributing child pornography. The accounts are reported to the Twitter Safety account, and the offending accounts are usually removed quickly, but the sheer volume is staggering. Over 31 accounts within a two hour period were discovered and reported by a handful of people. Over a 24 hour period, I counted 72 reported accounts between WhatsApp, Instagram, and Twitter.
Children and their parents unknowingly facilitate and exacerbate the problem of child pornography distribution. Parents that don’t monitor their child’s social media accounts or prohibit account creation won’t know if their child is posting pictures or video where they are scantily clad or in a sexually suggestive manner that will be saved by offenders and posted to various social media platforms.
I’m sure the motivations differ for why the members of these pedophile hunting groups have chosen to participate and volunteer a lot of time. The people I’ve spoken to are motivated by having families of their own or have a conviction to help, and they found pedophile hunting to be their niche.
Law enforcement
I can’t speak for all participants in these pedophile operations, but the people I spoke to didn’t use illegal means to obtain information on offenders. The OpChildSafety group discourages members from harassing and violating the privacy of offenders by collecting information that is publicly available then connecting the dots. The UK is cracking down on “vigilante” pedophile hunting groups because of the problems they are causing.
According to an article in The Times, “Police have been told to crack down on pedophile-hunting vigilantes after the number of groups in the nation targeting online child abusers rose to more than 75.” The article goes on to say, “Internal guidance for detectives, obtained by The Times, tells them to investigate any potential offenses by the hunters as well as those they accuse of trying to groom children.”
I reached out to several police departments across the country asking them a few simple questions.
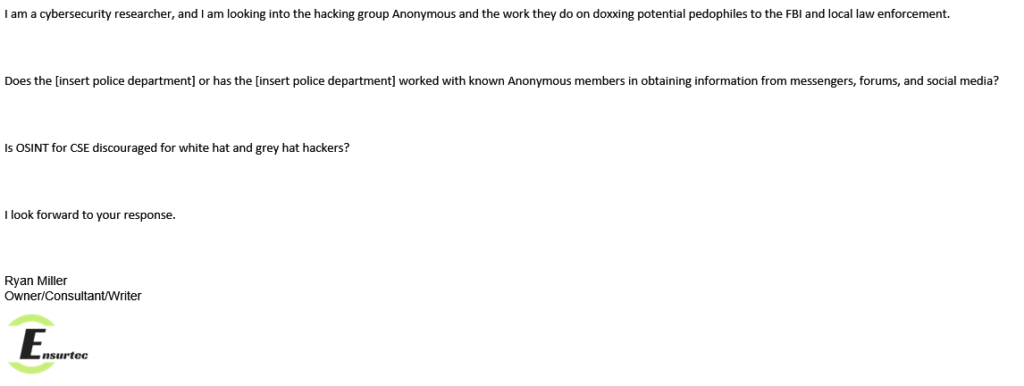
After one week only two of the six police departments responded. One of the police departments stated, “Our agency has not worked with any known members of Anonymous to conduct any sort of cyber investigations. Also, we do not have any SOP or Directive that discourages the use of Open Source Intel,” which is the best response one could hope for. Unfortunately, the other police department was on the opposite side of the spectrum by stating, “We do not work with Anonymous or any other Hacktivist group. As law enforcement, we cannot encourage any illegal hacking of any type.”
I sent a follow-up email to the second police department response. I explained what OSINT is and that no illegal hacking is taking place, but they have yet to respond and I’m not holding my breath. It’s disappointing when a single phrase (hacking group Anonymous) can derail a conversation because of a preconception.
Beyond pedophilia
The overarching mission for team OpChildSafety is in its name – the general safety of all children. Unfortunately, pedophilia is just the tip of the iceberg. Zoophilia is commonly encountered, and you can find signs of human trafficking. Zoophilia is reported as is any criminal sexual act that includes a child, but human trafficking is difficult to prove on social media even if there is evidence.
The best indication of trafficking is a child posted on several different accounts over a period that is not retweets or repeated posts as if they were being passed around.
Twitter’s failure
I reached out to CEO Jack Dorsey and COO Anthony Noto for information on how Twitter is handling the large volume of accounts that are distributing child pornography. Unsurprisingly, I haven’t received a response.
Twitter has been under fire for several years for not policing accounts that post or request child pornography. It appears that Twitter isn’t taking the steps that Facebook is, albeit not perfect when it comes to policing criminal content. Accounts are removed only when someone reports them.
The URL to report child sexual exploitation on Twitter, VIne, and Periscope is https://help.twitter.com/forms/cse.
After reporting a user, you will receive this email:
At least Twitter has created a reporting system and works with law enforcement, but the reporting method is passive. Twitter must create an active system for finding child exploitation accounts.
Reporting
If you see something, say something.
- The Internet Watch Foundation: anonymously report child sexual abuse content and non-photographic child sexual abuse images.
- Telegram messenger: [email protected]
- National Center for Missing and Exploited Children: the nation’s clearinghouse & comprehensive reporting center for all issues related to the prevention of and recovery from child victimization, NCMEC leads the fight against abduction, abuse, and exploitation – because every child deserves a safe childhood.
- Twitter: Twitter strives to provide an environment where people can feel free to express themselves. If abusive behavior happens, we want to make it easy for people to report it to us.
- Facebook: the best way to report abusive content or spam on Facebook is by using the Report link that appears near the content itself.
Success stories
Success stories have been trying to come by, not because of a lack of success, but because no one is willing to share information. I reached out to the OpChildSafety Support Group, and the only thing you could hear was crickets – on the Internet.
I sent out the tweet below that was retweeted and increased the number of impressions by 100 fold, but nothing came of it.
https://twitter.com/Milwizzle/status/955807000859959296
The only story I’ve been able to obtain is about a man in Houston Texas that possessed hundreds of images of child pornography at his home. The tip to the police department was received from the National Center for Missing and Exploited Children that came from a pedophile hunting team member.
You can read the full story here.